Modern ships demand reliable connectivity for safety, efficiency, and crew welfare. However, maritime environments present unique challenges:
- Limited terrestrial coverage: 5G signals fade ~5 miles offshore; 4G reaches ~28 miles.
- Satellite issues: High latency and limited bandwidth.
- Growing data needs: Ship operations and crew usage increased by 131% and 149% (2021-2022).
- Regulatory pressures: Ships must manage increasing operational data to meet over 20,000 pages of regulations.
Scalable networks address these problems by combining technologies:
- Hybrid connectivity: Integrates 5G, satellite (LEO, MEO, GEO), and vessel-to-vessel relays.
- Network slicing: Prioritizes critical operations over less urgent traffic.
- Edge computing: Processes data onboard, reducing satellite dependency.
- Modular designs: Allow cost-effective upgrades without overhauling systems.
NT Maritime leads with solutions offering:
- Speeds up to 220 Mbps (download) and 40 Mbps (upload).
- Latency under 99ms.
- Crew welfare tools like video calling and Telehealth.
Key takeaway: Scalable networks transform ships into connected hubs, ensuring efficient operations, better crew experiences, and compliance with modern demands.
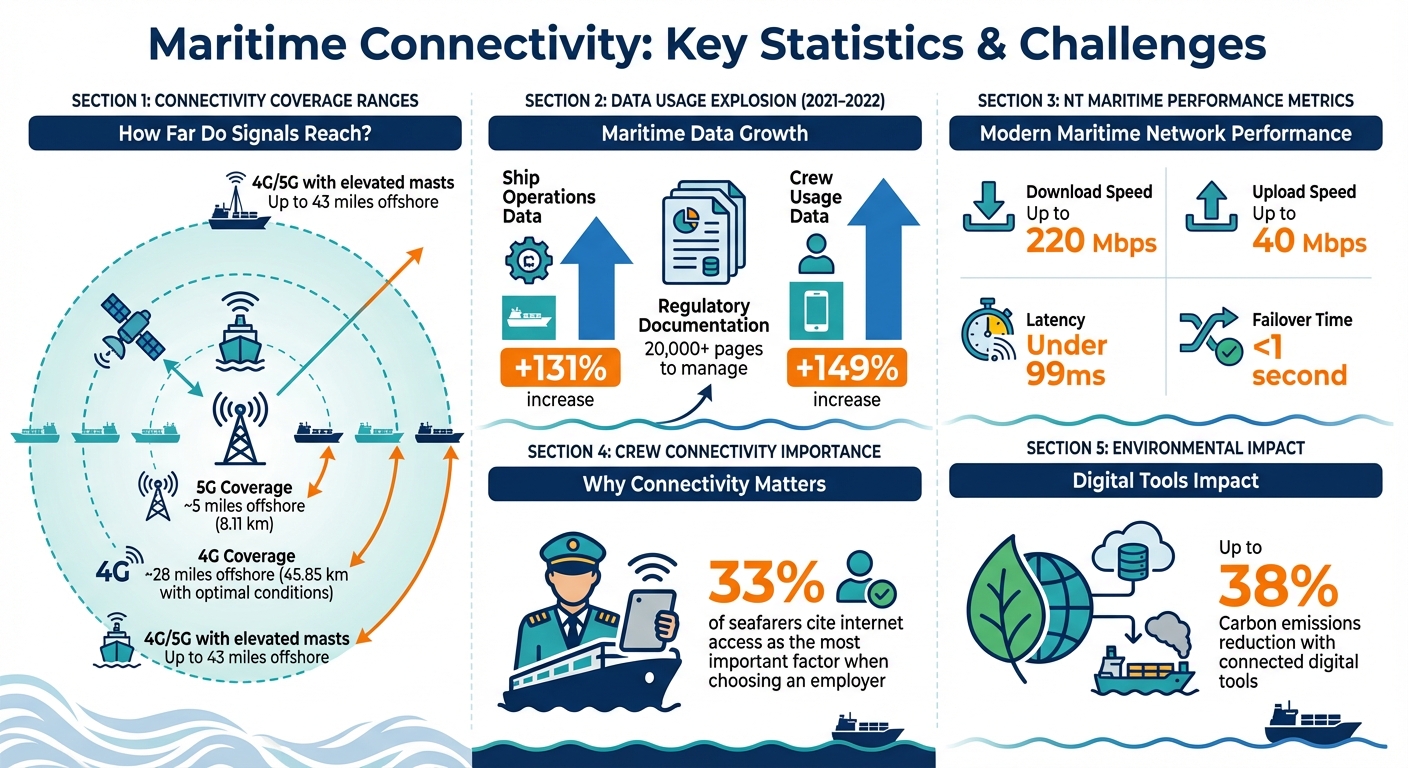
Maritime Connectivity Statistics: Network Coverage, Data Growth, and Performance Metrics
Marlink – delivering smart hybrid network solutions for shipping companies
sbb-itb-bda822c
Assessing Current Ship Connectivity Needs
Before upgrading any ship’s connectivity, start by documenting all existing onboard assets. This means taking stock of every piece of connectivity hardware, from satellite terminals to Wi-Fi access points. Your inventory should include VSAT (GEO) systems, newer LEO constellations like Starlink or OneWeb, and L-Band safety backups such as FleetBroadband or Iridium Certus. Don’t overlook terrestrial components like 4G/5G cellular setups, which, when paired with marine-grade antennas and signal boosters, are vital for coastal operations. These systems typically provide coverage up to 19 miles offshore, but with higher masts, this range can extend to 43 miles. A thorough inventory of all hardware types will lay the groundwork for a scalable connectivity strategy.
Inventory Network Components
Go beyond basic hardware and include specialized maritime systems that handle critical data. This means cataloging systems such as AIS (Automatic Identification System), GNSS (Global Navigation Satellite System), GMDSS (Global Maritime Distress and Safety System) equipment, Dynamic Positioning computers, industrial Ethernet switches, routers, and ship gateways that connect various systems. High-bandwidth devices like radars, cameras, and LiDAR sensors generate large files, which can put significant strain on your network’s transmission capacity. Additionally, emerging technologies such as unmanned surface vehicles (USVs), autonomous underwater vehicles (AUVs), and tethered UAVs may act as mobile relays or data collectors.
During your audit, pay close attention to antenna heights. Raising mast height is one of the simplest and most effective ways to extend the range of non-satellite connections. Also, identify any single points of failure – like a lone router or gateway – that could disrupt connectivity for the entire vessel.
Classify Applications and Traffic
Once your inventory is complete, assess how each asset supports different network demands. Divide traffic into four main categories: Operational (navigation and safety), Business (machinery analytics and logistics), Situational Awareness (sensor data), and Crew/Passenger welfare. Safety-critical data, such as GMDSS communications, should take top priority, followed by low-latency control and business applications. Crew and passenger traffic generally operates on a "best effort" basis unless specific retention goals require otherwise. Welfare services, such as NT Maritime’s Telehealth and onboard calling, are increasingly important, with 33% of seafarers now citing internet access as the most important factor when choosing an employer.
Set Scalability Goals
Establish clear objectives for bandwidth, latency, and resilience to meet both current and future demands. For example, autonomous ship operations require latency under 0.5 milliseconds to support real-time collision avoidance. High-throughput ship-to-shore uplink connections – ranging from 1 to 10 Mbps – are critical for transmitting sensor data, high-definition video for remote surveys, and situational awareness feeds. Your network should also be capable of switching between active and standby links (e.g., LTE to satellite) in under one second to avoid service interruptions. Additionally, ensure compliance with updated Maritime Labour Convention (MLC) requirements, which mandate internet access for seafarers.
As Neil Giles, Chief Technology Officer at Petredec Pte. Limited, explains: "The ultimate goal is to provide [crews] with the same level of connectivity that they get at home".
Designing a Scalable Onboard Network Architecture
Creating a network that can grow and adapt to the ever-changing demands of maritime environments requires a thoughtful and flexible design. By combining modular frameworks, hybrid connectivity, and onboard technology, ships can achieve reliable and efficient communication systems.
Use a Modular Network Design
A modular network structure divides the ship’s system into three layers: access, distribution, and core. This setup allows for seamless upgrades or expansions in specific areas without disrupting the entire network. Introducing an abstraction layer between OSI Layers 2 and 3 makes it possible to reroute, duplicate, or prioritize traffic across cellular, satellite, and Wi-Fi networks without interrupting active sessions. This ensures uninterrupted application performance, even when the network switches from LTE to VSAT mid-session.
Software-Defined Networking (SDN) takes this modularity further by replacing traditional hardware with programmable software. This flexibility allows adjustments to radio frequencies and modulation in real time, adapting to changing maritime conditions. For example, a Multi-RAT Gateway (MRGW) can handle multiple Radio Access Technologies, enabling dynamic traffic management between LTE, 5G, and VSAT based on current availability. Additionally, modern 5G systems use "splits" between the Radio Access Network (RAN) and the core, allowing lightweight user planes to operate onboard while centralizing control functions.
Integrate Hybrid Connectivity Solutions
Combining satellite, cellular, and Wi-Fi mesh technologies creates a robust network with redundancy and automated failover capabilities. A centralized gateway can monitor real-time wireless metrics – like RSRP and RSRQ – and automatically select the best connection based on location and signal quality. For example, in coastal areas, 4G at 700 MHz can cover distances up to 45.85 km from shore, while 5G at 3.5 GHz offers higher bandwidth but typically covers only about 8.11 km. Bonding multiple WAN sources, such as Starlink and LTE, boosts speed and ensures high availability. If the primary connection fails, a backup can take over in less than a second.
For vessels navigating open waters, a multi-hop architecture can extend 5G coverage by using other ships as relays. This approach reduces reliance on costly satellite bandwidth while maintaining connectivity, especially for fleets following the same routes. Chris Sepp, Vice President of IT at Atlas Corp. (Seaspan), highlights that breaking the perception of maritime connectivity as bandwidth-limited opens the door to scalable digital solutions for fleets with over 200 vessels. NT Maritime also uses hybrid connectivity to sustain crew welfare services.
Plan for Onboard Wireless and Edge Computing
Wi-Fi mesh networks onboard distribute satellite or mobile connections throughout the ship, supporting crew welfare, passenger needs, and IoT devices like sensors and beacons. Edge computing, which processes data locally on the ship, reduces reliance on satellite or cloud connections. This setup is critical for real-time applications like AI-driven navigation and IoT-enabled engines, minimizing latency for safety systems and engine monitoring.
Modern edge infrastructure uses modular nodes, making it easy to upgrade RAM, CPU, or storage without disrupting operations. Zero-Touch Provisioning (ZTP) simplifies deployment, allowing non-technical crew members to plug in hardware that configures itself via the cloud, cutting installation time by up to 90%. Running communication gateways as virtual machines enhances compatibility and ensures consistent performance from shore-based labs to onboard edge clusters. This approach also prepares the network for future advancements, such as 6G or additional Low Earth Orbit (LEO) satellite constellations.
| Feature | Function | Onboard Wireless Role |
|---|---|---|
| Edge Computing | Local data processing & storage | Connects devices & distributes data |
| Connectivity | Operates autonomously (offline) | Links users/IoT to backhaul |
| Scalability | Modular hardware upgrades | Expands mesh & increases access points |
| Benefit | Zero latency for critical systems | Improves crew welfare & IoT mobility |
Implementing Security, QoS, and Reliability in Scalable Networks
In scalable networks, it’s essential to secure critical systems and maintain performance, even during failures. For maritime environments, downtime isn’t just inconvenient – it can jeopardize safety and disrupt operations. By integrating security measures, Quality of Service (QoS), and redundancy from the outset, networks can grow without sacrificing reliability. Let’s explore how to implement these elements to create a resilient maritime network.
Prioritize Traffic with QoS Policies
Certain types of traffic, like telehealth video calls, need to take priority over routine updates. That’s where QoS comes in – it determines which data packets get transmitted first, reducing packet loss, jitter, and latency during peak usage. By categorizing traffic (e.g., VoIP, video, telemetry), the network ensures critical services maintain high performance, even when bandwidth is stretched.
Use 802.1Q CoS tagging for Layer 2 and DSCP markings for Layer 3 to classify and prioritize traffic based on importance. Scheduling algorithms can further optimize performance: reserve Strict Priority for emergency traffic while using Weighted Round Robin (WRR) for general traffic to balance resources. Abstraction layers can also reroute or prioritize traffic seamlessly across satellite, cellular, and Wi-Fi interfaces without interrupting active sessions.
| PCP Value | Priority | Traffic Type | Recommended Use Case |
|---|---|---|---|
| 7 | 7 (Highest) | Network Control | Routing protocols and network management |
| 6 | 6 | Internetwork Control | Critical network signaling |
| 5 | 5 | Voice (VO) | VoIP; Telehealth voice calls (<10ms latency) |
| 4 | 4 | Video (VI) | Real-time surveillance; Telehealth video (<100ms latency) |
| 3 | 3 | Critical Applications | Shared Situational Awareness (SSA) data |
| 0 | 1 (Lowest) | Best Effort | General internet and non-critical updates |
Source: IEEE recommendations for Priority Code Point (PCP)
For the most critical functions, like routing protocols, assign the highest priority (PCP 7). Telehealth voice calls should use PCP 5, while video traffic like surveillance or telehealth video calls can be prioritized at PCP 4. Routine internet browsing or background updates should remain at the lowest priority (PCP 0).
Build Redundancy into the Network
Redundancy is key to avoiding single points of failure. A hierarchical network design – divided into Core, Distribution, and Access layers – ensures predictable traffic patterns and simplifies troubleshooting. Redundant Layer 3 interconnections can recover from failures in as little as 60–200 milliseconds.
Technologies like EtherChannel or 802.3ad combine multiple physical links into a single logical path, boosting resilience. To further enhance reliability, terminate links on separate hardware. For endpoint connectivity, use redundancy protocols like HSRP or GLBP, which can converge in under a second.
Additional safeguards include redundant power supplies, CPUs, and supervisor engines. Stateful Switchover (SSO) and Non-Stop Forwarding (NSF) technologies maintain Layer 3 forwarding during supervisor failures, typically recovering in 1–3 seconds. For backhaul connectivity, combine multiple technologies like satellite (LEO/MEO/GEO), 5G/LTE, and vessel-to-vessel relays. Bandwidth bonding can aggregate these connections, ensuring both failover and increased throughput. Backup links can take over in less than a second if the primary connection fails.
Avoid daisy-chaining fixed-configuration switches, which can create routing issues. Instead, use stacking technologies like VCStack or StackWise, or deploy modular chassis to reduce complexity. For the fastest failover performance, rely on hardware-based link failure detection rather than software timers.
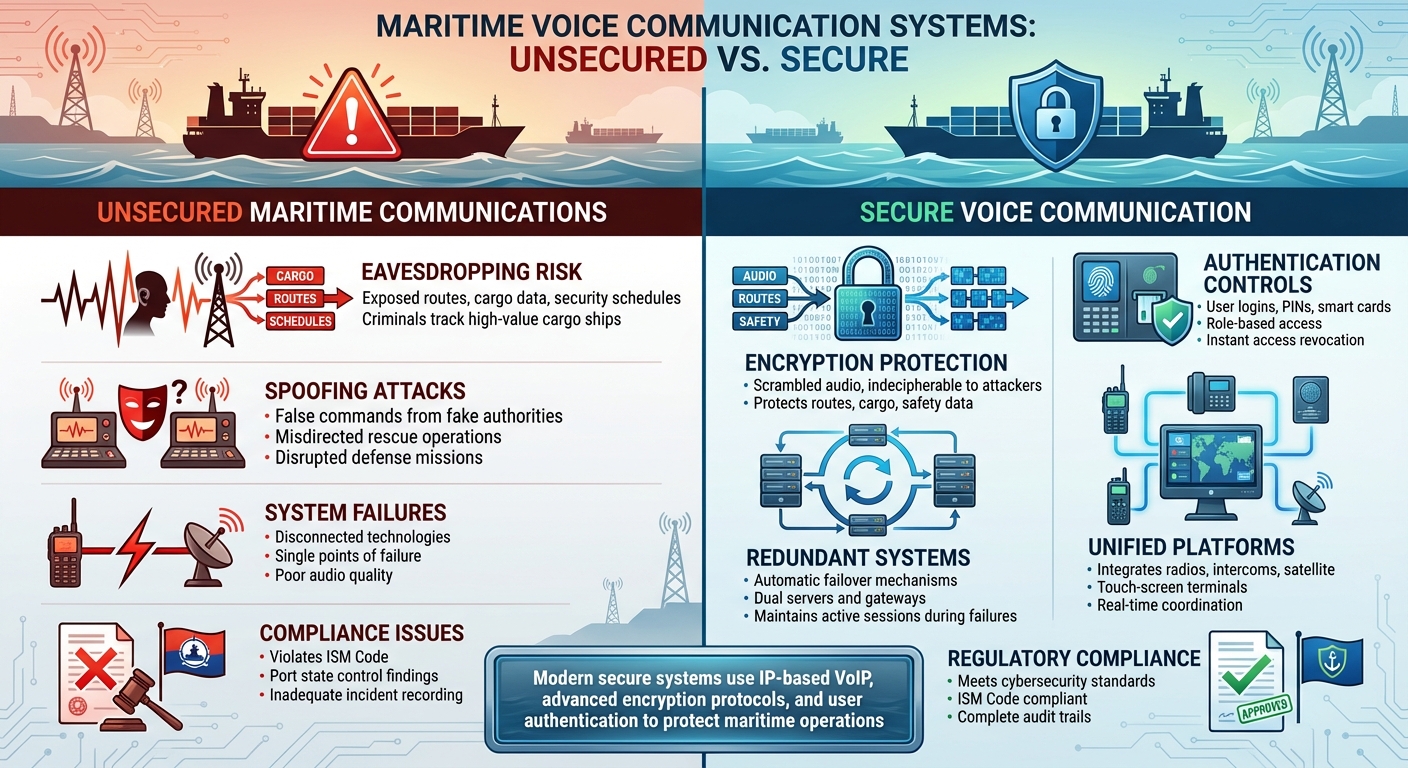
Enforce Security and Compliance Standards
While redundancy ensures connectivity, robust security safeguards your network from threats. Maritime networks face unique cybersecurity challenges due to their operation in international waters, connections to multiple networks, and the mix of operational technology (OT), crew systems, and passenger services they host. Traditional perimeter-based defenses are no longer enough. Instead, adopt a Zero Trust Architecture to protect resources regardless of their location.
"Zero trust assumes there is no implicit trust granted to assets or user accounts based solely on their physical or network location (i.e., local area networks versus the internet) or based on asset ownership."
NT Maritime’s systems align with federal and military cybersecurity guidelines to reinforce these principles. Network segmentation plays a critical role by isolating essential maritime operations from other traffic. For example, separate LANs can be used for business systems (e.g., email, PMS), crew services (prepaid internet), and M2M/custom services (e.g., ECDIS, VDR). This ensures that a compromised device cannot access critical navigation or engine control systems. Role-Based Access Control (RBAC) further limits access to sensitive areas, granting permissions only to authorized personnel.
To secure data in transit, use Virtual Private Networks (VPNs) between vessels and shore, protecting communications across various WAN links (VSAT, cellular, satellite). For remote access to OT systems, deploy secure firewalls and robust remote access solutions to safeguard both port and ship infrastructure.
Comply with NIST SP 800-207 standards to protect individual resources rather than entire network segments. As remote users and cloud-based assets grow in number, this approach becomes increasingly critical. Automate failover processes using network management devices capable of switching between hardware and multiple WAN links (VSAT, 4G/5G, L-band) without manual intervention, eliminating single points of failure. Lastly, ensure compliance with NIS2 standards to maintain comprehensive visibility and security across all industrial network components.
Scaling and Monitoring the Network Over Time
Once your network is up and running, the focus shifts to maintaining its performance, scaling operations effectively, and integrating emerging technologies. The demand for maritime data continues to grow, and without vigilant monitoring and adaptable infrastructure, networks can quickly become overwhelmed.
Centralized Monitoring and Management
Centralized platforms streamline fleet connectivity by offering a single dashboard to manage everything. These systems provide real-time insights into data usage, hardware performance, and SIM connectivity. They also enable automated traffic management. For instance, Multi-RAT Gateways (MRGW) can dynamically switch between LTE and VSAT networks based on current channel conditions, ensuring each application gets the best possible connection.
A notable example comes from January 2023, when researchers from Gachon University and SyncTechno Inc. tested an MRGW on the Korean Autonomous Surface Ship (KASS) testbed near Ulsan, South Korea. The system seamlessly switched between LTE and VSAT networks within one second of detecting a disconnection, maintaining uninterrupted real-time video streaming. This was achieved using REST APIs and SNMP for wireless monitoring, verified through the DX Ocean remote monitoring platform.
Centralized systems also bring significant cost savings. Techniques like Delta Synchronization reduce data usage by transmitting only the changes in files. High-quality connectivity enables shoreside technicians to troubleshoot remotely, cutting down on expensive physical interventions.
Chris Sepp, Vice President of IT at Atlas Corp. (Seaspan), explains: "All of our ships are deployed to generate revenue. We don’t have the luxury of having regular physical access to them in drydock, so the majority of shoreside interventions need to be performed remotely".
This kind of centralized management provides the foundation for scaling your network in a data-driven way.
Use Metrics and Automation for Scaling
Making informed decisions starts with tracking the right metrics. Key indicators like latency (measured in milliseconds), jitter, packet loss, throughput (Mbps), and total data consumption help you stay ahead of potential issues. For example, Starlink’s maritime plans, which range from 50 GB to 2 TB, require careful monitoring to avoid overage fees or throttled speeds. Metrics also ensure that critical tools, such as ERP systems or video conferencing, continue to perform well even during times of high usage.
| Metric Category | Key Parameters | Purpose |
|---|---|---|
| Performance | Latency (ms), Jitter (ms), Packet Loss (%) | Maintain stability for real-time apps like VoIP and video |
| Utilization | Throughput (Mbps), Load per Carrier | Optimize hybrid network routing |
| Consumption | Total Data (GB/TB), Usage per User/App | Control costs and prevent throttling |
| Reliability | Uptime (%), Signal Strength (dB) | Ensure SLA compliance and link stability |
Automation is another game-changer. In November 2025, Northern Marine Group, a division of Stena, cut its fleet software compliance time by 92%, reducing it from six months to just two weeks. Led by DevSecOps Manager Scott Mungall, the team replaced manual CD-mailing with the Resilio Platform‘s automated data distribution over VSAT. This enabled multi-gigabyte updates to reach vessels even in low-bandwidth regions like the Indian Ocean.
Automation also supports proactive scaling by setting thresholds for CPU, memory, and storage usage. These thresholds can trigger alerts or even auto-scaling before performance suffers. SD-WAN orchestration further enhances efficiency by routing traffic based on application priority and link quality, ensuring critical services always get the best connection.
By leveraging these tools and metrics, you can ensure your network remains scalable and resilient.
Future-Proof with Modular Upgrades
To keep up with changing demands, modular upgrades make it easy to expand your network without overhauling the entire system. Node-based clusters combine compute, storage, and networking into units that can be added incrementally as capacity needs grow. Software-Defined Infrastructure (SDI) adds another layer of flexibility by abstracting hardware, allowing resources to be dynamically allocated across the fleet without relying on cloud services. This approach eliminates the need for costly system replacements – new nodes simply integrate into the existing setup.
Tools like Terraform and Ansible automate provisioning, ensuring consistent configurations across multiple vessels and reducing the risk of manual errors. Zero-touch provisioning takes this a step further, allowing for hardware replacements or network expansions without requiring on-site IT staff. Standardizing hardware and software across the fleet simplifies troubleshooting, reduces training time, and speeds up deployment through pre-configured templates.
Tore Morten Olsen, President of Maritime at Marlink, highlights: "The maritime industry is on the brink of a technological step change, driven by low Earth orbit (LEO) satellite connectivity, cloud-based platforms, and artificial intelligence".
With modular designs, your network can easily adapt to new technologies, whether that’s next-generation satellite systems, 5G-Advanced, or AI-powered applications, without starting from scratch.
Conclusion
The importance of scalable networks in maritime operations cannot be overstated – they drive efficiency, enhance crew well-being, and provide a competitive edge. Recent trends highlight this shift: between June 2021 and June 2022, crew-related data usage skyrocketed by 149%, while business application usage grew by 131%. These numbers reveal how ships are transforming into hubs of connectivity, reshaping life and work at sea.
Scalable network architectures play a key role in optimizing voyages, cutting down port waiting times, and reducing fuel consumption. Connected sensors further enhance operations by enabling predictive maintenance, which prevents costly equipment failures before they occur. Additionally, digital tools integrated into these networks can significantly lower carbon emissions – by as much as 38% – helping the maritime sector meet IMO 2030 goals. For seafarers, connectivity is no longer a luxury but a necessity. In fact, 33% of seafarers now prioritize internet access over pay and leave when choosing an employer, underscoring its role in crew retention.
NT Maritime’s communication solutions are at the forefront of this transformation. Offering secure, high-speed internet (up to 220 Mbps download and 40 Mbps upload with latency under 99ms) and integrated communication systems, their technology supports both commercial and government/military needs. These solutions enable everything from crew video calls with loved ones to real-time HD surveillance and telemedicine services. With NT Maritime, vessels are equipped to tackle today’s challenges while preparing for tomorrow’s opportunities.
FAQs
How do scalable networks improve connectivity and crew well-being on ships?
Scalable networks transform ship connectivity by seamlessly integrating satellite, LTE, and land-based links, delivering fast, dependable, and cost-efficient internet access. This means crew members can enjoy smooth video calls, streaming services, and social media, making life onboard more connected and comfortable.
Beyond personal use, these networks play a critical role in supporting essential services like telehealth consultations, real-time weather updates, and cloud-based tools, all of which enhance safety and operational efficiency. NT Maritime takes this a step further by providing secure, unified communication systems that adapt to fleet size, ensuring both crew well-being and operational priorities are met.
How does edge computing enhance ship connectivity?
Edge computing transforms ship connectivity by handling data processing directly on the vessel. This approach reduces the need to depend on high-latency satellite links. Tasks such as AI-powered navigation, predictive maintenance, and passenger services can be managed locally, which helps cut delays, saves bandwidth for essential communications, and keeps sensitive data securely onboard.
By pairing edge computing with flexible network setups, ships can maintain critical services like crew communication, onboard calls, and telehealth applications – even when shore-based cloud connections are disrupted. It also enables real-time decisions for improving fuel efficiency, optimizing routes, and enhancing safety systems. NT Maritime incorporates edge-enabled infrastructure into its offerings, ensuring ships have dependable, high-speed internet and communication tools, no matter the conditions.
What are the benefits of hybrid connectivity for ship communication networks?
Hybrid connectivity blends satellite networks – such as LEO, GEO, and L-Band – with terrestrial 4G/5G cellular connections. This setup allows vessels to automatically select the most efficient and cost-effective network available at any given moment. By dynamically switching or dividing traffic between networks, it ensures a stable connection without interrupting user activity.
Near shore, this system reduces latency by prioritizing faster cellular signals. Once the vessel moves into open waters, it seamlessly transitions to satellite networks. This not only keeps costs down by favoring cheaper options when possible but also guarantees consistent internet access. For ship operators, this means smoother video calls, reliable crew-to-shore communication, and continuous telemetry for navigation and safety systems.
NT Maritime leverages hybrid connectivity to deliver secure, high-speed internet, onboard calling, and integrated communication services – keeping passengers and crew connected regardless of their location.