The IMO Cyber Risk Guidelines are essential for safeguarding modern ships from digital threats. These guidelines integrate cyber risk management into existing safety systems, ensuring ships remain secure and operational. Here’s what you need to know:
- Focus Areas: Identify, protect, detect, respond, and recover from cyber threats.
- Compliance: Since January 2021, shipowners must include cyber risk management in their Safety Management Systems (SMS) as part of annual audits.
- Key Systems: Navigation, propulsion, and communication systems are critical areas of focus.
- Training: Crew and shore-based staff need regular training to handle cyber risks effectively.
- Secure Networks: Communication systems must be hardened against threats, with measures like firewalls and network segmentation.
The guidelines align with frameworks like the NIST Cybersecurity Framework and emphasize integrating cybersecurity into daily maritime operations. Ships built after July 1, 2024, must meet stricter requirements under IACS Unified Rules.
These measures aim to reduce vulnerabilities, ensuring safe and secure shipping in an increasingly connected world.
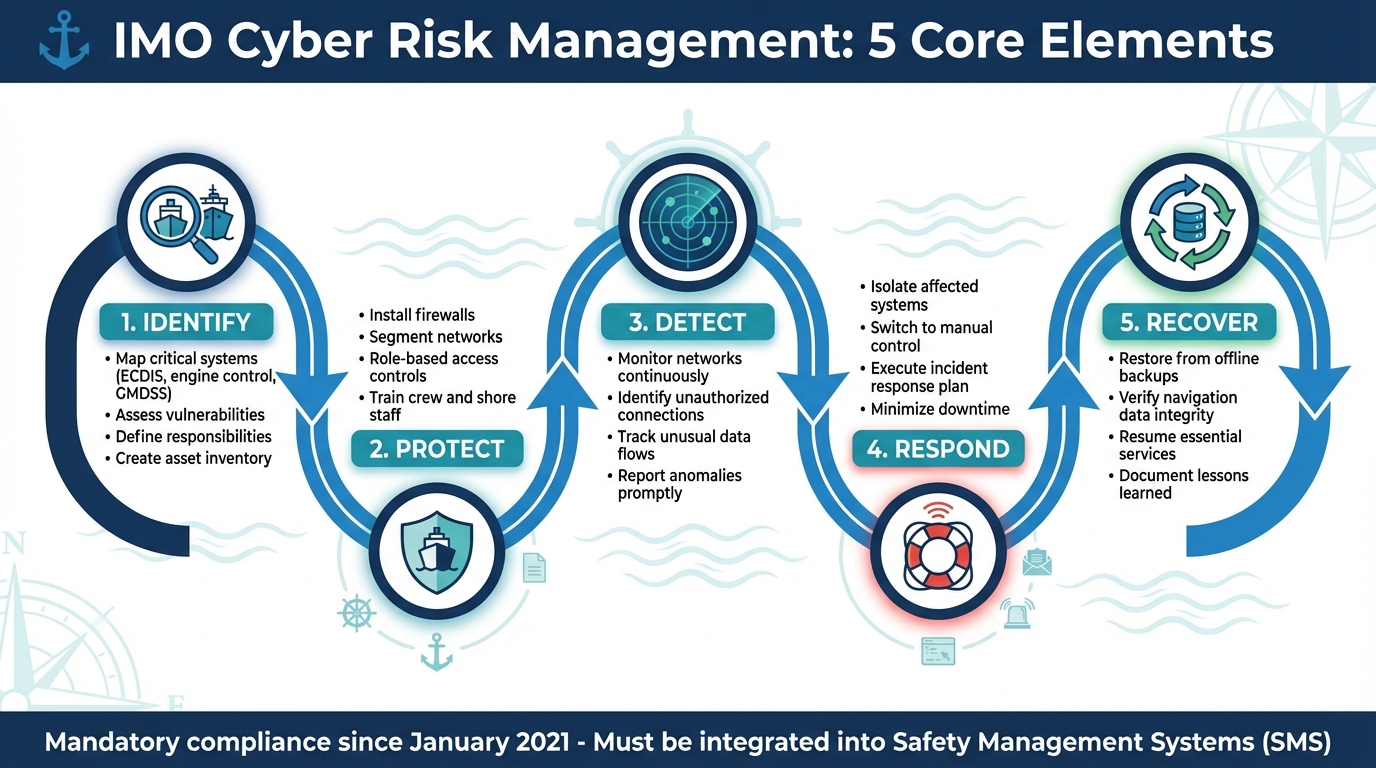
IMO Cyber Risk Management Framework: 5 Core Elements for Maritime Security
Port IT – Compliance with IMO 2021 cybersecurity rules
Core Elements of Cyber Risk Management
The IMO framework is built around five key elements: Identify, Protect, Detect, Respond, and Recover. Together, these elements form a structured approach to tackling the specific cyber risks faced by maritime operations. In this environment, even a single cyber incident could jeopardize critical systems like navigation, propulsion, or communications – systems essential for crew safety and vessel security.
"Cyber risk management means the process of identifying, analysing, assessing and communicating a cyber-related risk and accepting, avoiding, transferring or mitigating it to an acceptable level, considering costs and benefits of actions taken to stakeholders." – IMO
To be effective, these elements should be seamlessly integrated into the vessel’s existing Safety Management System, rather than treated as standalone requirements. This ensures that managing cyber risks becomes a natural part of daily operations. Below, we break down how these elements translate into practical steps onboard.
Risk Identification and Assessment
The first step is identifying all critical assets that, if compromised, could disrupt a ship’s operations. This includes evaluating vulnerabilities in key systems such as navigation (ECDIS), propulsion (engine control), and communications (GMDSS). Operators also need a clear understanding of who is responsible for managing these risks and how interconnected systems might amplify the impact of a breach. For instance, a vulnerability in one system could trigger cascading effects, leading to operational, safety, or security issues.
Protection and Detection Measures
Protection centers on putting technical safeguards in place to block unauthorized access. These measures might include installing firewalls, segmenting networks to isolate critical systems, and setting up role-based access controls. For example, keeping navigation systems separate from general-use networks can help prevent malware from spreading across the vessel.
Detection involves real-time monitoring to identify unauthorized connections or unusual data flows. Establishing procedures for continuous monitoring and prompt anomaly reporting is essential to reduce potential damage. While preventive measures aim to stop breaches, detection ensures swift identification of threats, helping to minimize their impact.
Incident Response and Recovery
When a cyber event occurs, having a well-defined response plan is critical to reducing downtime and ensuring the safety of the vessel. Response steps should include isolating affected systems and switching to manual control of critical functions, such as engine operation. Recovery efforts focus on restoring systems using offline backups and verifying the integrity of critical data, particularly for navigation systems. Quickly resuming essential services is key to maintaining operational resilience.
| Functional Element | Maritime Application |
|---|---|
| Identify | Map critical systems: navigation (ECDIS), propulsion (engine control), communications (GMDSS). |
| Protect | Install firewalls, segment networks, implement role-based access controls, train crew. |
| Detect | Monitor networks for unauthorized connections and unusual activity. |
| Respond | Isolate affected systems and maintain manual control of essential functions. |
| Recover | Restore systems from offline backups and verify navigation data integrity. |
Compliance Requirements
Meeting IMO guidelines involves embedding cyber risk management into your Safety Management System (SMS), training your team, and strengthening your infrastructure. Building on the basics of risk management, compliance requires thorough documentation, focused training, and robust network security.
Cyber Security Plan Documentation
Cybersecurity documentation must be integrated into your SMS under the ISM Code. This documentation should address the five core elements: Identify, Protect, Detect, Respond, and Recover.
- Identify: Clearly outline personnel roles, responsibilities, and maintain an inventory of critical systems, assets, and data essential to ship operations.
- Protect: Detail risk control measures, mitigation strategies, and contingency plans.
- Detect: Include steps to identify cyber incidents quickly and effectively.
- Respond: Provide plans for restoring compromised systems to ensure safe operations.
- Recover: Define backup and restoration procedures to minimize downtime.
"The resolution encourages administrations to ensure that cyber risks are appropriately addressed in existing safety management systems… no later than the first annual verification of the company’s Document of Compliance after 1 January 2021." – IMO Resolution MSC.428(98)
Shipowners must not only document cyber risks but also analyze and address them. Guidance from organizations like BIMCO and frameworks such as the NIST Cybersecurity Framework can serve as useful templates to structure these elements. This documentation forms the foundation for effective training and operational resilience.
Training and Awareness Programs
Human error plays a significant role in cybersecurity incidents. To address this, your training program should be built into the SMS and cater to two groups: shipboard crew and shore-based personnel. Just as technical defenses safeguard systems, well-trained individuals are crucial for identifying and responding to threats.
Training for the crew should cover recognizing system vulnerabilities, understanding attack methods, implementing preventive measures, and executing incident response protocols. Shore-based staff should focus on identifying sensitive information and applying general mitigation techniques. Flexible learning options, such as computer-based training (CBT), can help seafarers stay up-to-date with evolving threats.
An effective training program should evolve continuously, incorporating lessons learned from past incidents or near misses. This ongoing process ensures that crews remain prepared to tackle new cyber challenges.
Secure Communication Networks
Securing communication networks is the final step in turning your documented controls and trained responses into a resilient operational framework. Communication systems are critical for safe ship operations, and IMO guidelines emphasize the need to harden these networks against cyber threats while aligning with the five core elements of risk management. For ships with contracts signed after July 1, 2024, communication systems must comply with IACS Unified Requirements E26 and E27, ensuring secure integration of both Operational Technology (OT) and Information Technology (IT) equipment.
"The URs (maritime cyber security regulations) will apply to everything computer-based on board such as… communications systems including public address systems, and navigation systems – anything that is integral to making the ship move, navigate and operate safely." – DNV
As data exchange increases, secure communication networks are becoming indispensable. NT Maritime provides advanced IT and communication solutions tailored for maritime needs. Their offerings include encrypted onboard calling, secure messaging, and high-speed internet with download speeds of up to 220 Mbps. These solutions not only help operators meet compliance standards but also ensure reliable connectivity.
To maintain secure networks, operators should embed security measures into systems from the design phase through daily operations. Third-party suppliers must also play a role in ensuring network integrity. A multi-layered security approach should be applied to critical communication and navigation systems.
sbb-itb-bda822c
Alignment with Industry Standards
The IMO guidelines are rooted in core cybersecurity principles and are designed to work seamlessly with other maritime standards, simplifying the process of managing cyber risks. By understanding these connections, operators can adopt effective security measures without duplicating efforts. Let’s explore how these standards come to life in practice.
NIST Cybersecurity Framework Alignment
The IMO Guidelines align closely with the five core functions of the NIST Cybersecurity Framework – Identify, Protect, Detect, Respond, and Recover. This alignment allows operators to embed cyber risk management directly into their Safety Management System (SMS). Here’s how each function translates into actionable practices:
- Identify: Classify systems based on their impact on safety and maintain a risk register within your SMS.
- Protect: Use technical measures like asset management and vulnerability assessments to safeguard systems.
- Detect: Deploy monitoring tools to identify anomalies in real time.
- Respond: Establish clear incident response plans with defined roles and responsibilities.
- Recover: Develop a Plan of Actions & Milestones to quickly restore operations after a cyber incident.
"The recommendations can be incorporated into existing risk management processes and are complementary to the safety and security management practices already established by IMO." – International Maritime Organization
ICS Cyber Security Top 10
While the IMO guidelines provide a broad framework, organizations like the International Chamber of Shipping (ICS) and BIMCO offer detailed technical guidance for implementation. The IMO emphasizes that its recommendations complement existing practices and should be used alongside resources like the ICS "Guidelines on Cyber Security on board Ships."
The ICS guidance dives deeper into technical controls and compliance procedures, ensuring a more tactical approach. Collaboration among key maritime organizations – such as BIMCO, WSC, INTERTANKO, and INTERCARGO – fosters a unified strategy for addressing cyber risks. This collective effort also enhances the integration of cyber risk management into Ship Security Plans, bolstering overall operational resilience.
Integration into Ship Security Plans
Incorporating cyber risk management into Ship Security Plans requires a tailored, risk-based approach. This involves assessing your specific technology assets and adapting measures accordingly. In June 2017, the Maritime Safety Committee adopted Resolution MSC.428(98), formally linking cyber risk management to the International Safety Management (ISM) Code. This shift has embedded cyber risks as a core element of operational safety, rather than a separate concern.
Operators should conduct a gap assessment to evaluate their current security measures against IMO and NIST standards. This evaluation lays the groundwork for a mitigation roadmap, pinpointing areas that need improvement. Focus on systems within your SMS, categorizing them by their potential impact on safety and the marine environment. Update your documentation to include Cyber Risk Management procedures directly within your SMS and Ship Security Plans. The ultimate aim is operational resilience – ensuring vessels can continue safe operations even under cyber threat.
Meeting Compliance and Building Cyber Resilience
Adhering to IMO cyber risk requirements is not just about ticking regulatory boxes – it’s about safeguarding operations against threats that could jeopardize safety, security, and business continuity. Compliance with IMO Resolution MSC.428 is mandatory, requiring companies to integrate cyber risk management into their Safety Management System (SMS) by the first annual verification of their Document of Compliance. But compliance alone isn’t enough. To truly protect modern vessels, both Information Technology (IT) and Operational Technology (OT) must be addressed.
Modern ships are highly connected, relying on integrated systems for everything from bridge control and propulsion to power management and communication networks. These systems often exchange data with shore-based infrastructure for purposes like decarbonization tracking and improving operational efficiency. While this connectivity boosts performance, it also opens the door to potential cyber vulnerabilities.
Secure communication systems are a critical line of defense in this interconnected ecosystem. As cyber technologies underpin systems essential for safety and security, robust protocols are needed to shield critical functions – like navigation, propulsion, and emergency response – from data breaches or corruption. NT Maritime offers advanced secure communication networks tailored for maritime operations, ensuring compliance and operational resilience through encrypted ship-to-shore connections that meet stringent federal and military standards.
Beyond secure communication, operators must address internal vulnerabilities to build true resilience. While network security is foundational, proactive measures such as regular assessments and implementing technical safeguards are key to ensuring uninterrupted operations. Cyber resilience involves more than meeting regulatory requirements; it’s about maintaining continuity even under threat. This includes conducting gap analyses to uncover weak points, creating formal risk registers within the SMS, and deploying safeguards like network segmentation and firewalls. Increasingly, Port and Flag States are enforcing these practices during inspections, and non-compliance can lead to legal and operational setbacks.
"The overall goal is to support safe and secure shipping, which is operationally resilient to cyber risks." – International Maritime Organization
The maritime industry is shifting its perspective on cybersecurity, moving from treating it as a standalone IT concern to embedding it within the broader safety culture. Aligning with established frameworks like the NIST Cybersecurity Framework and IACS Unified Requirements (UR E26 and E27, mandatory for vessels contracted for construction on or after July 1, 2024) allows operators to streamline compliance while fortifying their defenses. As the industry evolves, integrating cybersecurity into daily operations and safety management systems is no longer optional – it’s essential.
FAQs
What are the main components of the IMO Cyber Risk Management Framework?
The IMO Cyber Risk Management Framework provides a structured approach to strengthening cyber defenses within maritime Safety Management Systems. It’s built around five essential components:
- Identify: Take inventory of all digital systems, both on ships and onshore. Evaluate potential threats and pinpoint vulnerabilities that could disrupt operations, compromise safety, or weaken security.
- Protect: Put safeguards in place to reduce risks. This includes measures like access controls, encryption, secure communication protocols, and crew training to prevent cyber incidents.
- Detect: Keep a close watch on systems with continuous monitoring and anomaly detection tools to quickly spot any signs of cyber threats.
- Respond: Have a clear plan ready for addressing incidents. This should include steps for containment, communication, and mitigation to limit the impact.
- Recover: Focus on restoring systems to normal as quickly as possible while using the experience to improve future risk management strategies.
These steps align with internationally recognized standards such as ISO/IEC 27001 and the NIST Framework for Critical Infrastructure. For U.S.-based maritime operators, tools like NT Maritime’s secure communication solutions – offering encrypted voice and video calls – play a key role in supporting the Protect and Detect stages by ensuring data security and enabling real-time threat monitoring.
How do the IMO Cyber Risk Guidelines align with the NIST Cybersecurity Framework?
The IMO Cyber Risk Management Guidelines closely mirror the NIST Cybersecurity Framework by emphasizing five core functions: Identify, Protect, Detect, Respond, and Recover. This shared structure makes it easier for maritime operators to align key practices – like maintaining asset inventories, conducting threat assessments, and creating incident response plans – with NIST’s well-established framework.
For fleets operating in the U.S., this alignment streamlines compliance with both federal and industry cybersecurity standards. It allows operators to leverage familiar tools, metrics, and reporting formats. Companies like NT Maritime offer solutions such as secure onboard networks and real-time monitoring systems that meet the requirements of both IMO and NIST, ensuring a strong and cohesive approach to managing cyber risks.
What are the cyber risk compliance requirements for ships built after July 1, 2024?
Ships built on or after July 1, 2024, will need to comply with the International Association of Classification Societies’ (IACS) Unified Requirements E26 and E27. These rules focus on implementing onboard cyber risk management and resilience strategies to safeguard the safety and security of newly classified vessels.
The goal of these requirements is to tackle the increasing cybersecurity challenges faced by the maritime industry while aligning with updated international standards for secure operations.

